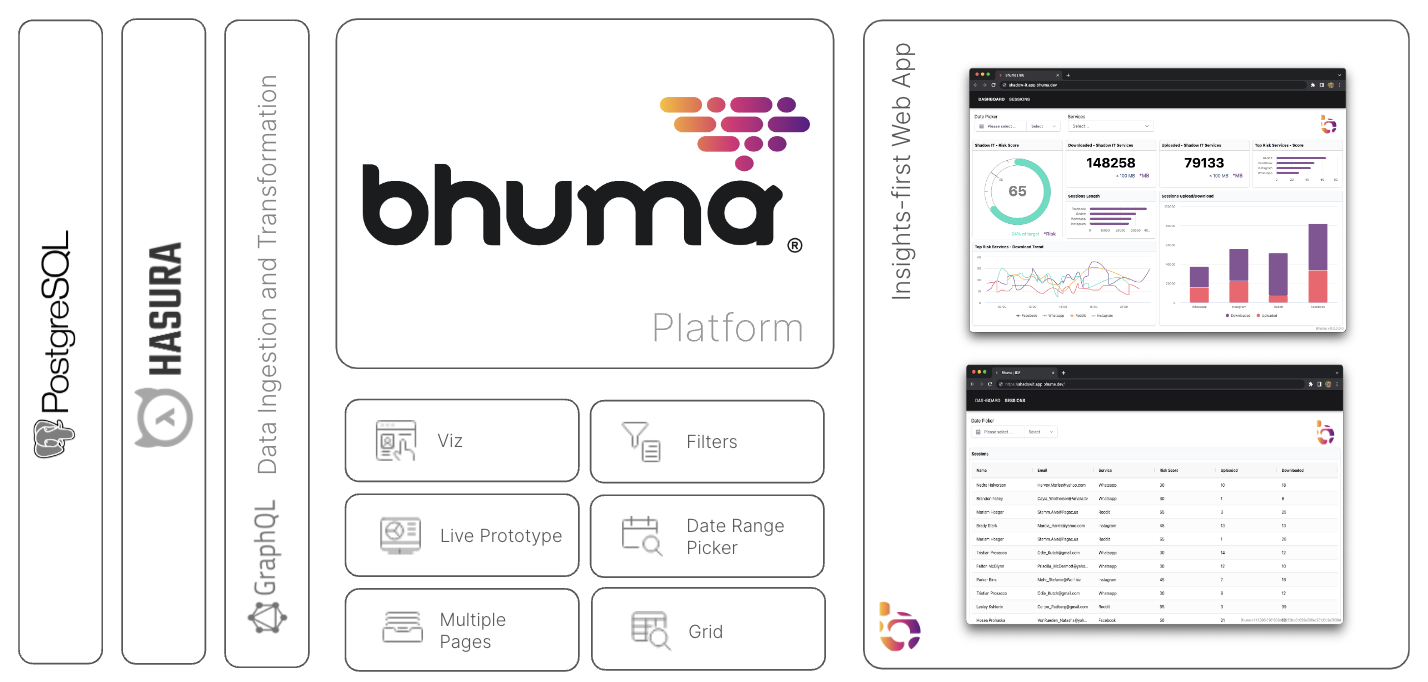
Hasura + Postgres
Shadow IT Management App
Learn how Bhuma's Platform can help you bring clarity to your shadow IT management with an actionable dashboard. Unlock the power of data-driven insights and decisions that will move your organization forward!
Shadow IT
Refers to the unauthorized use of information technology resources in an organization. It is a security risk because it can lead to data breaches and other cybersecurity threats. Therefore, organizations should clearly understand what constitutes shadow IT and how to prevent it.
Updated about 1 year ago
